Japanese component manufacturing titan Shimano is believed to be the victim of a ransomware attack by the LockBit group.
A screenshot reportedly from the LockBit leak site, uploaded on Thursday evening UTC, shows that the hackers claim to have access to 4.5 TB of the organisation’s data, including highly sensitive information including:
- Confidential employee details – including social security numbers, residential addresses, and passport scans
- Financial documents – including balance sheets, budget, bank statements, cashflow and tax details
- Client database – including contact details, reports, minutes from meetings, factory inspection results, incident reports, and legal documents
- Confidential diagrams and drawings, laboratory tests, NDAs, contracts, and development materials.
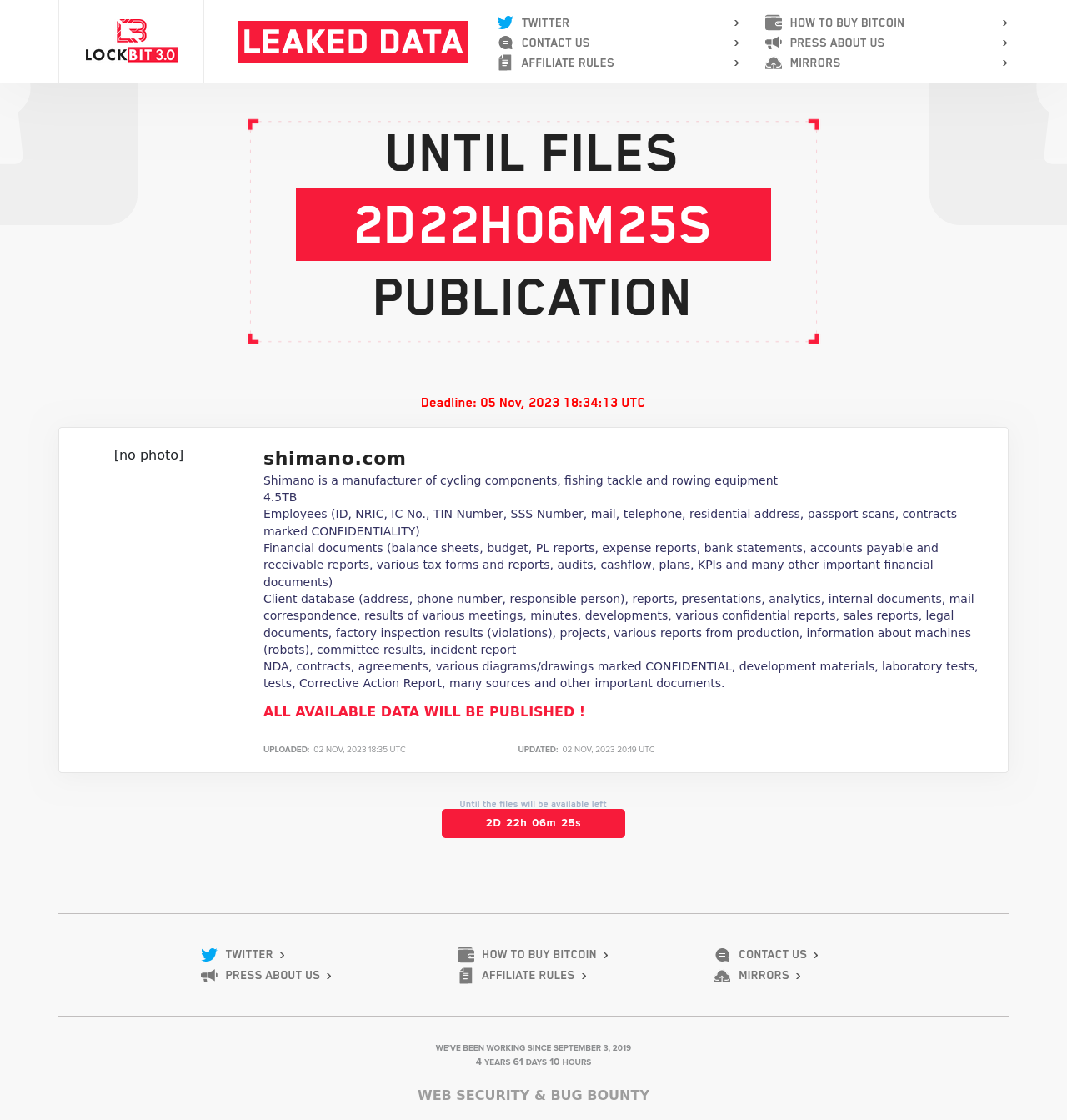
The screenshot is consistent with other examples perpetrated by the LockBit group. Separate screenshots accessed by Escape Collective show Shimano listed on the ransom website of the LockBit 3.0 variant. LockBit leak sites usually exist on the dark web – in this case on the Tor network – with the targets of their attacks contacted with a demand for ransom payment by a certain deadline. Shimano's deadline is November 5, 18:34PM UTC – just under three days from now.
Contacted by Escape Collective, a European Shimano representative confirmed that “HQ is aware of the suspected attacks and an investigation is underway.” A separate response from a US representative said that “this is an internal matter at Shimano and we cannot comment on anything at this time.” There does not appear to be any disruption to Shimano’s websites currently, and Shimano did not respond to questions about the ransom amount or any current impact to its operations.
LockBit is the world’s dominant ransomware group – accounting for 27.93% of all known ransomware attacks last financial year – and has been active since 2019, releasing a number of variants of its ransomware in that time. It operates as a Ransomware-as-a-Service group, selling its services to cybercriminals who target companies, but has also recently developed a bug bounty program offering rewards to people who report vulnerabilities to the group that can later be exploited.
When a LockBit ransomware attack is executed, it usually takes the form of multifaceted extortion – firstly by locking down company files, secondly by threatening to release confidential data, and occasionally extending threats to third parties related to the company, or launching a service disruption. Apart from the immediate threat to a targeted company’s operations, there is also the risk of identity theft, industrial espionage or information falling into the hands of rivals; LockBit accepts payments not just from the victim, but third parties as well.
The group claims to be located in the Netherlands, although it is suspected to originate in eastern Europe or Russia. Three Russian nationals have previously been charged by the US Department of Justice for alleged participation in LockBit’s operations, and the group conspicuously does not attack Russian powers or allies. The Department of Justice has described LockBit as the creator of "one of the most active and destructive ransomware variants in the world."

Shimano, which has a net worth of US$13.5 billion and some 11,000 employees, is a high-profile victim of the group, although it’s far from the only such entity to fall into LockBit’s trap. Aeronautics giant Boeing is currently being extorted by the group, with LockBit claiming that “a tremendous amount of sensitive data was exfiltrated and ready to be published if Boeing do not contact within the deadline!” EvilCorp, the perpetrators of the 2020 Garmin hack, are also LockBit affiliates. Past high-profile LockBit ransom demands have been in the millions: Continental (2022) and Accenture (2021) were both extorted for US$50M, while in January the UK's Royal Mail was hit with a ransom demand of US$80M, and was forced to suspend international deliveries for some weeks. [It is not known whether the companies capitulated to LockBit's demands, whether they negotiated a lower rate, or whether they resolved the situation otherwise.]
As for Shimano, this is the latest challenge to overcome in what has already been a challenging year for the bicycle and fishing component market leader. Overall sales in the first nine months of 2023 in the cycling division have fallen by almost a quarter year-on-year, while operating income has fallen by almost half. The company is seen as a canary in the coalmine for the health of the bicycle industry more broadly, which experienced huge growth during the pandemic before cooling precipitously.
Shimano is also battling a PR crisis over the recall of 2.8 million Dura-Ace and Ultegra 11-speed cranksets globally. A class-action lawsuit was filed last month against the company, as well as Specialized and Trek, for "fraudulently concealing the defective crankset[s]" over a period of "years".
This is a developing story and will be updated with any further comment from Shimano.
For more about the variety of online threats posed to the cycling industry, see here for a long-read on the vast scam network targeting consumers, or here for the twisted story of a high profile Twitter hack.
Did we do a good job with this story?






